1 min read
5 Common Types of Social Engineering Attacks
Social engineering is one of the foremost ways that hackers and other bad actors will try and penetrate an organization's cybersecurity defenses....
4 min read
.jpg) Justin Brown
:
Jun 24, 2022 9:00:00 AM
Justin Brown
:
Jun 24, 2022 9:00:00 AM
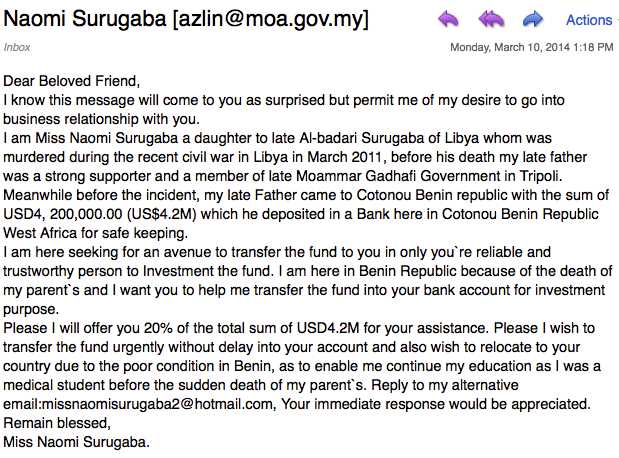
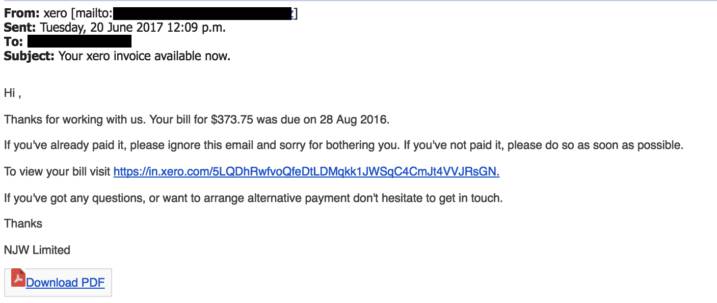
Phishing is one of the most common and well-known social engineering techniques. It's the process of sending emails (or texts, which is known as smishing) appearing to be from reputable sources in an attempt to get someone to reveal personal information.
These can take the form of emails seeming to come from coworkers, or impersonating reputable brands such as Google and Microsoft or government institutions such as the IRS. The idea is that you will see something familiar and won't look too closely.
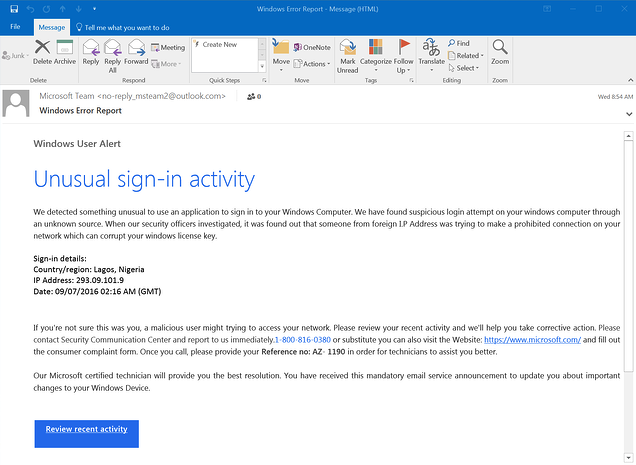
Source: Phishing Examples | Phishing.org
Phishing is a type of social engineering attack that seeks to collect personal information such as login credentials or credit card numbers by pretending to be a trustworthy entity. The attacker will typically send an email or message that appears to come from a reputable source, such as a financial institution or popular online service.
The message will often include a link that leads to a fake website that looks identical to the real thing. The user is then prompted to enter sensitive information, which is then collected by the attacker.
Phishing attacks can be difficult to detect, but there are several warning signs to look out for, such as suspicious links or email addresses, grammatical errors, and unexpected requests for personal information.
Source: The Most Common Examples Of A Phishing Email | uSecure
If you suspect that you may be the target of a phishing attack, do not respond to the message and immediately report it to your IT department or security team.
There are a few different types of phishing attacks, but the most common ones include:
There are several steps you can take to protect yourself from phishing attacks, including:
If you think you may have responded to a phishing email or clicked on a malicious link, there are a few steps you should take:
If you receive a phishing email or text, do not respond to it! You should report it to your IT department or security team immediately.
You can also report phishing emails to the FTC at ftc.gov/complaint. And if you get a text message that looks like phishing, forward it to SPAM (7726).
When in doubt, throw it out! If you're unsure about an email or text, don't take any chances. Delete it and move on. After all, it's just a message.
By being aware of the signs of phishing and taking steps to protect yourself, you can help keep your personal information safe from criminals.
Phishing is a well-known social engineering technique that uses emails (or texts) to try and get someone to reveal personal information. The goal of a phishing attack can be anything from getting you to open a malicious attachment, stealing your login credentials, to just plain stealing.
Source: Phishing Examples | Phishing.org
There are several steps you can take to protect yourself from phishing attacks, including keeping your software and antivirus up-to-date, being aware of the signs of a phishing email, and reporting any suspicious messages immediately.
If you think you may have responded to a phishing email or clicked on a malicious link, there are some things you should do immediately, such as changing your passwords and running a virus scan. It's important to remember that taking action is the best way to protect yourself from these types of attacks.
While phishing attacks are the most well-known type of social engineering attack, it's important to be aware of the other types of attacks that exist. By being informed and taking steps to protect yourself, you can help keep your personal information safe from criminals.
If you are interested in cybersecurity awareness training for your nonprofit organization, or would like to speak to our cybersecurity experts about your security, contact us here.

1 min read
Social engineering is one of the foremost ways that hackers and other bad actors will try and penetrate an organization's cybersecurity defenses....

Pretexting is a type of social engineering attack that is often used to gain access to confidential information. In a pretexting attack, the attacker...
"Ethical hacking" sometimes known as "white hat hacking" is similar in process to malicious hacking, but is100% legal. People who engage in ethical...